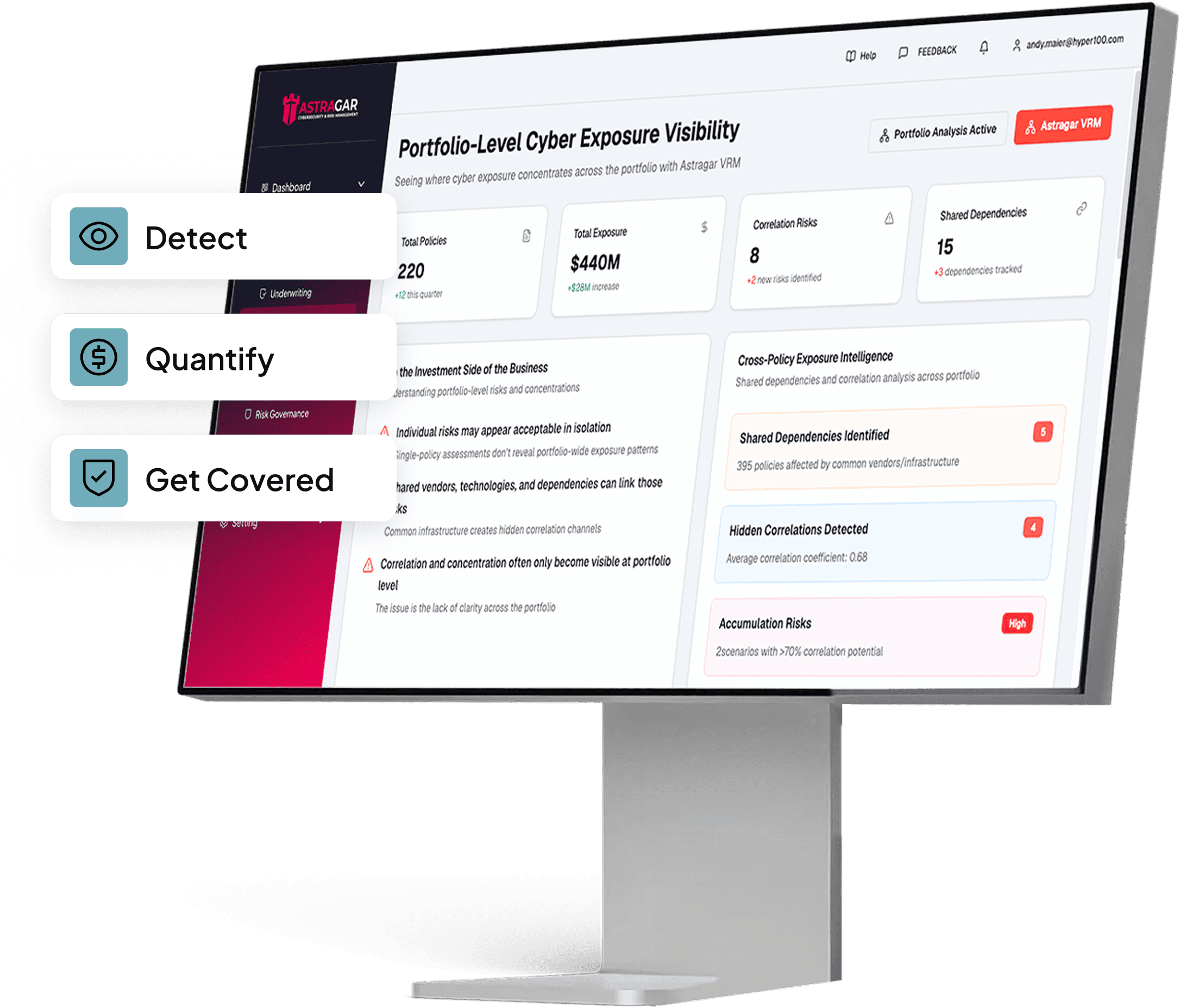
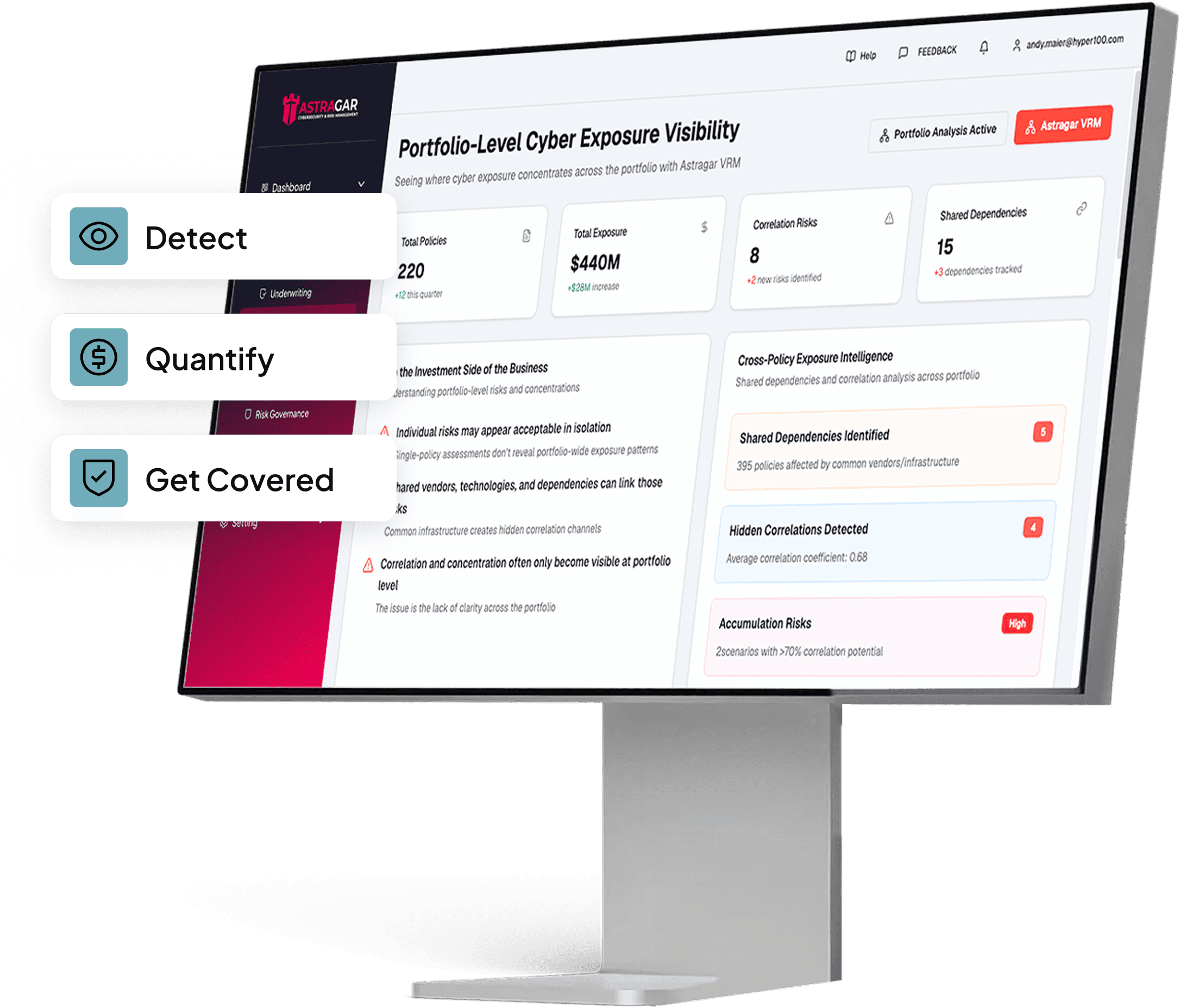
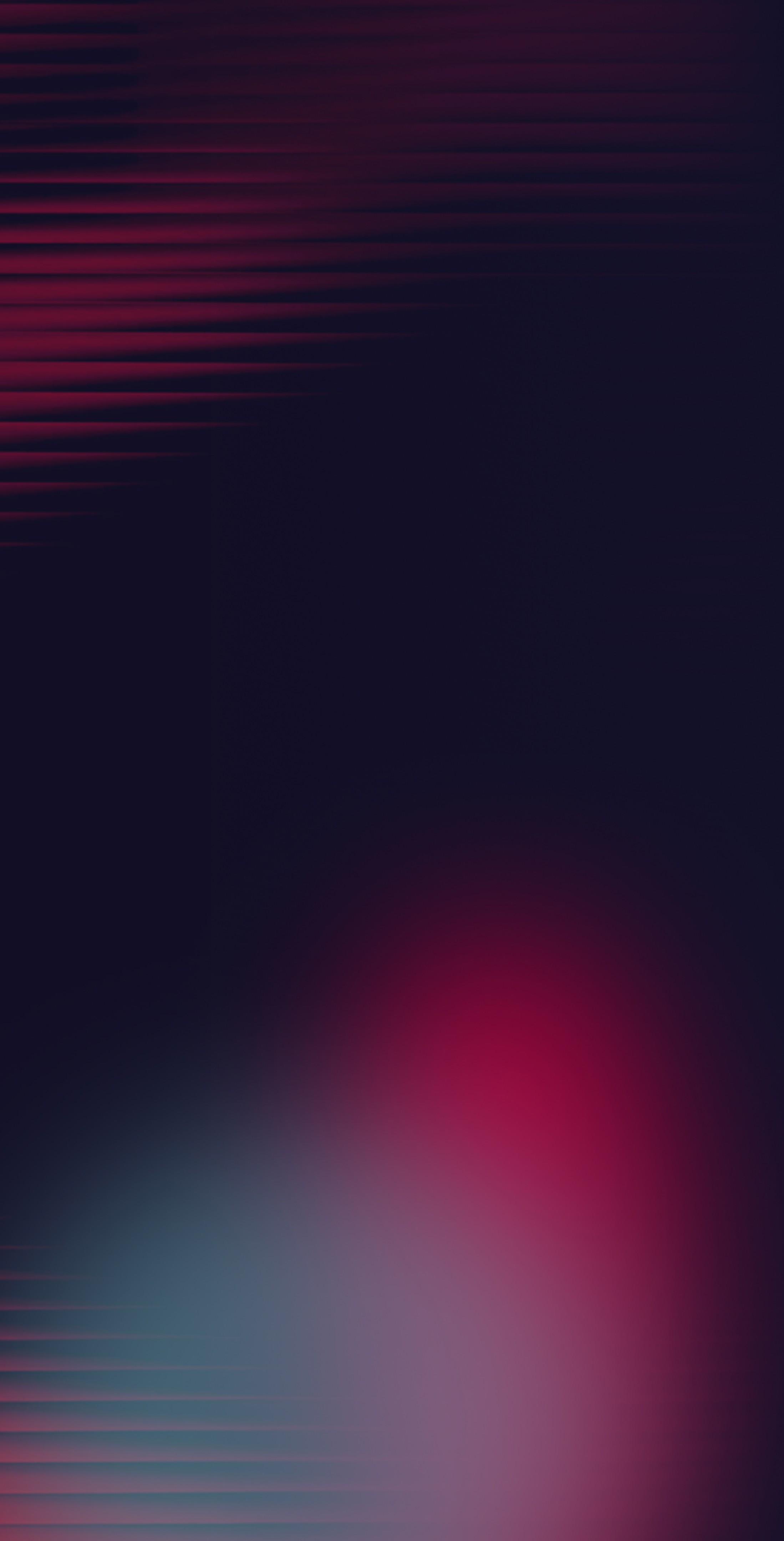
Cyber Insurance Should Prevent Breaches — Not Just Pay Claims.
Astragar reduces breach risk, not just insures against it — combining cyber risk quantification, GRC, and cyber insurance underwriting in one platform.
Cyber Insurance Should Prevent Breaches — Not Just Pay Claims.
Astragar reduces breach risk, not just insures against it — combining cyber risk quantification, GRC, and cyber insurance underwriting in one platform.
Cyber Insurance Should Prevent Breaches — Not Just Pay Claims.
Astragar reduces breach risk, not just insures against it — combining cyber risk quantification, GRC, and cyber insurance underwriting in one platform.
Platform capabilities
Platform capabilities
What the platform delivers
The platform turns raw vulnerability data into board-ready financial insight, regulator-ready submissions, and incident-ready response. Each capability is configured as part of a pilot or managed engagement.
Scanner integrations
Pull data automatically from leading commercial scanners, with custom connectors for your stack.
Scanner integrations
Pull data automatically from leading commercial scanners, with custom connectors for your stack.
Asset consolidation and prioritization
Identify critical third-party, concentration and shared dependency risks.
Asset consolidation and prioritization
Identify critical third-party, concentration and shared dependency risks.
Regulatory attestation
Collect evidence, attest, and submit to auditors and regulators across NYDFS, SOC 2, ISO 27001, and more.
Regulatory attestation
Collect evidence, attest, and submit to auditors and regulators across NYDFS, SOC 2, ISO 27001, and more.
Incident reporting
Produce regulator-ready incident reports via built-in adapters for NYDFS, SEC, DORA, GDPR, and state breach laws.
Incident reporting
Produce regulator-ready incident reports via built-in adapters for NYDFS, SEC, DORA, GDPR, and state breach laws.

End-to-End Solution
From Risk Identification to Full Coverage
01
Scan & Identify
VRM assessment scans vulnerabilities and maps them to financial risk
01
Scan & Identify
VRM assessment scans vulnerabilities and maps them to financial risk
02
Map & Comply
GRC engine maps controls to frameworks and generates compliance evidence
02
Map & Comply
GRC engine maps controls to frameworks and generates compliance evidence
03
Run Scenarios
Model breach scenarios with financial impact per threat — so you understand potential loss and make informed decisions
03
Run Scenarios
Model breach scenarios with financial impact per threat — so you understand potential loss and make informed decisions
04
Submit & Place
Underwriting-grade outputs flow to brokers and carriers for accurate quoting and placement
04
Submit & Place
Underwriting-grade outputs flow to brokers and carriers for accurate quoting and placement

End-to-End Solution
From Risk Identification to Full Coverage
01
Scan & Identify
VRM assessment scans vulnerabilities and maps them to financial risk
02
Map & Comply
GRC engine maps controls to frameworks and generates compliance evidence
03
Run Scenarios
Model breach scenarios with financial impact per threat — so you understand potential loss and make informed decisions
04
Submit & Place
Underwriting-grade outputs flow to brokers and carriers for accurate quoting and placement

End-to-End Solution
From Risk Identification to Full Coverage
01
Scan & Identify
VRM assessment scans vulnerabilities and maps them to financial risk
02
Map & Comply
GRC engine maps controls to frameworks and generates compliance evidence
03
Run Scenarios
Model breach scenarios with financial impact per threat — so you understand potential loss and make informed decisions
04
Submit & Place
Underwriting-grade outputs flow to brokers and carriers for accurate quoting and placement
Benefits
Benefits
Reduce Cyber Risk. Reduce Coverage Costs.
Breach Risk Reduction
Prioritise the vulnerabilities most likely to cause material business loss.
Breach Risk Reduction
Prioritise the vulnerabilities most likely to cause material business loss.
Breach Risk Reduction
Prioritise the vulnerabilities most likely to cause material business loss.
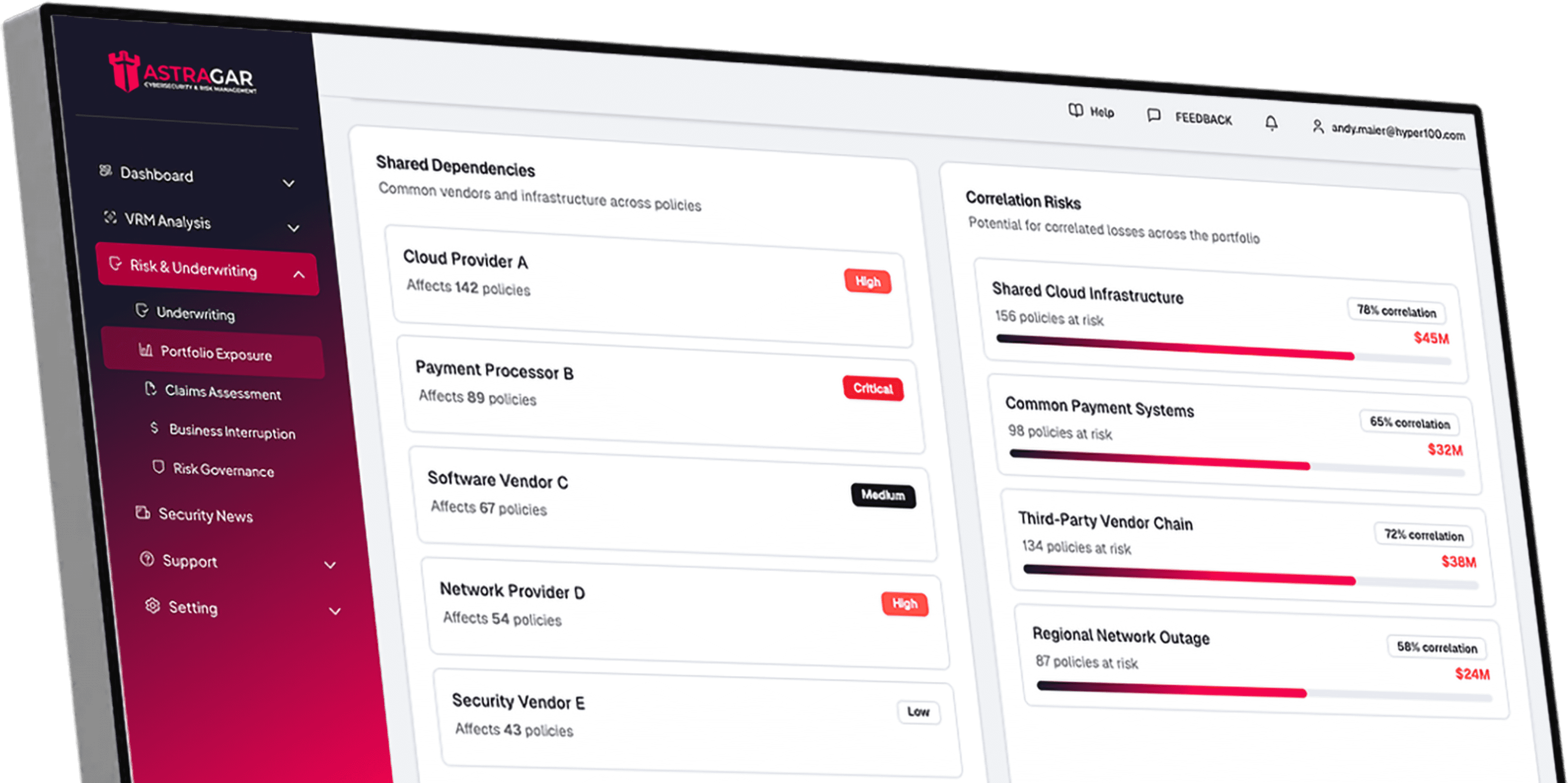
Vendor Visibility
Identify critical third-party, concentration and shared dependency risks.
Vendor Visibility
Identify critical third-party, concentration and shared dependency risks.
Vendor Visibility
Identify critical third-party, concentration and shared dependency risks.
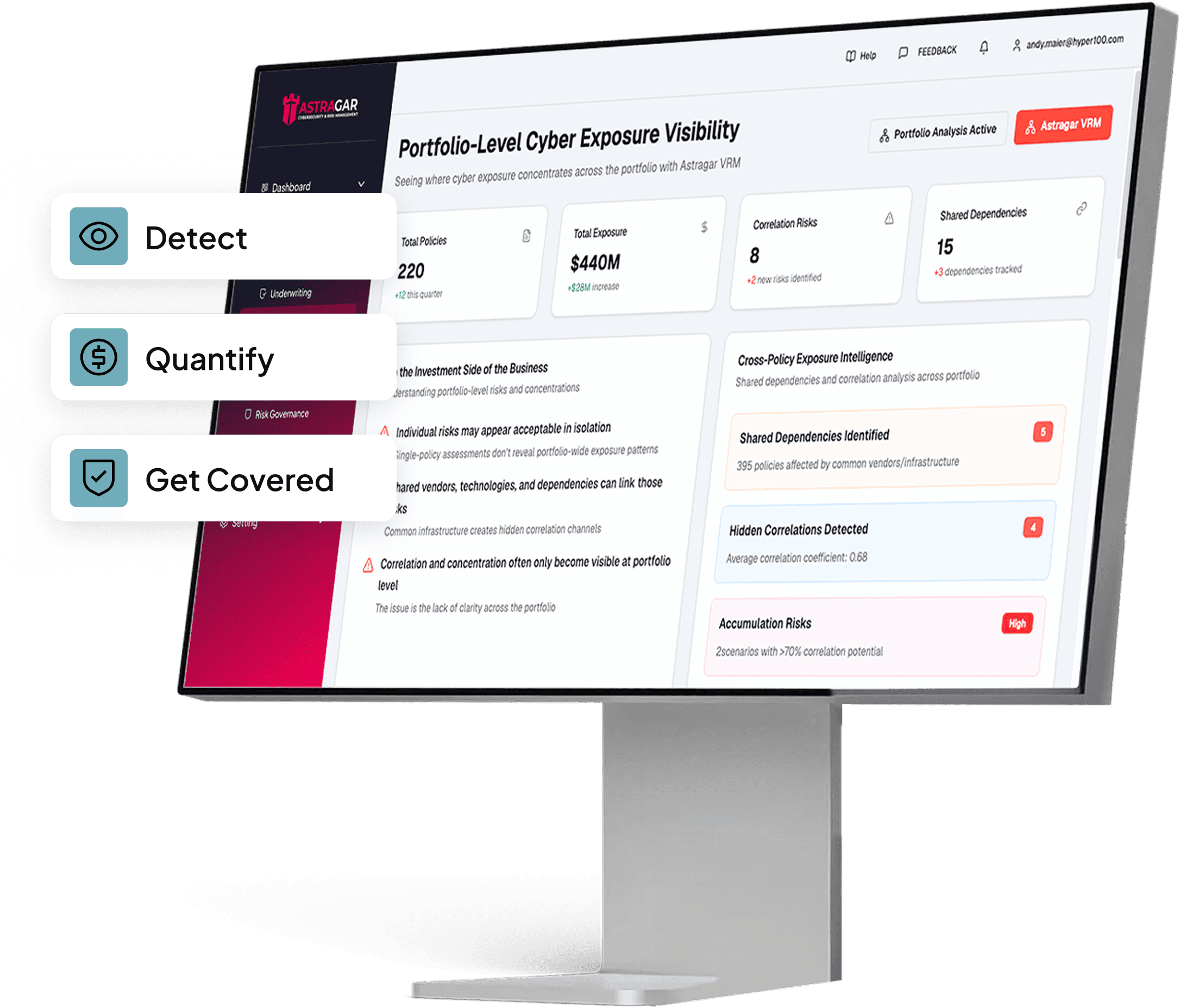
Regulatory Compliance
Map cyber risks to NIST, ISO, SOC 2, NYDFS 500 and DORA controls.
Regulatory Compliance
Map cyber risks to NIST, ISO, SOC 2, NYDFS 500 and DORA controls.
Regulatory Compliance
Map cyber risks to NIST, ISO, SOC 2, NYDFS 500 and DORA controls.
Better Insurance Outcomes
Evidence-based risk data drives sharper underwriting and stronger negotiation leverage at every renewal.
Better Insurance Outcomes
Evidence-based risk data drives sharper underwriting and stronger negotiation leverage at every renewal.
Better Insurance Outcomes
Evidence-based risk data drives sharper underwriting and stronger negotiation leverage at every renewal.
AI-POWERED FUNCTIONALITIES
AI-POWERED FUNCTIONALITIES
Everything You Need to Assess and Manage Cyber Risk
Vendor Risk Management
Vendor Risk Management
Scan & Quantify Vulnerabilities
Scan & Quantify Vulnerabilities
Scan & Quantify Vulnerabilities
Understand your risk in financial terms. Monitor continuously, prioritize what matters, and produce risk scores trusted by leadership and insurers.
Understand your risk in financial terms. Monitor continuously, prioritize what matters, and produce risk scores trusted by leadership and insurers.
Understand your risk in financial terms. Monitor continuously, prioritize what matters, and produce risk scores trusted by leadership and insurers.

Controls Assessment
Controls Assessment
Verify Controls.
Quantify Gaps
Verify Controls.
Quantify Gaps
Verify Controls.
Quantify Gaps
Go beyond checkbox compliance. Astragar verifies whether your controls actually work against the scenarios that matter, and tells you the dollar cost of each gap.
Go beyond checkbox compliance. Astragar verifies whether your controls actually work against the scenarios that matter, and tells you the dollar cost of each gap.
Go beyond checkbox compliance. Astragar verifies whether your controls actually work against the scenarios that matter, and tells you the dollar cost of each gap.
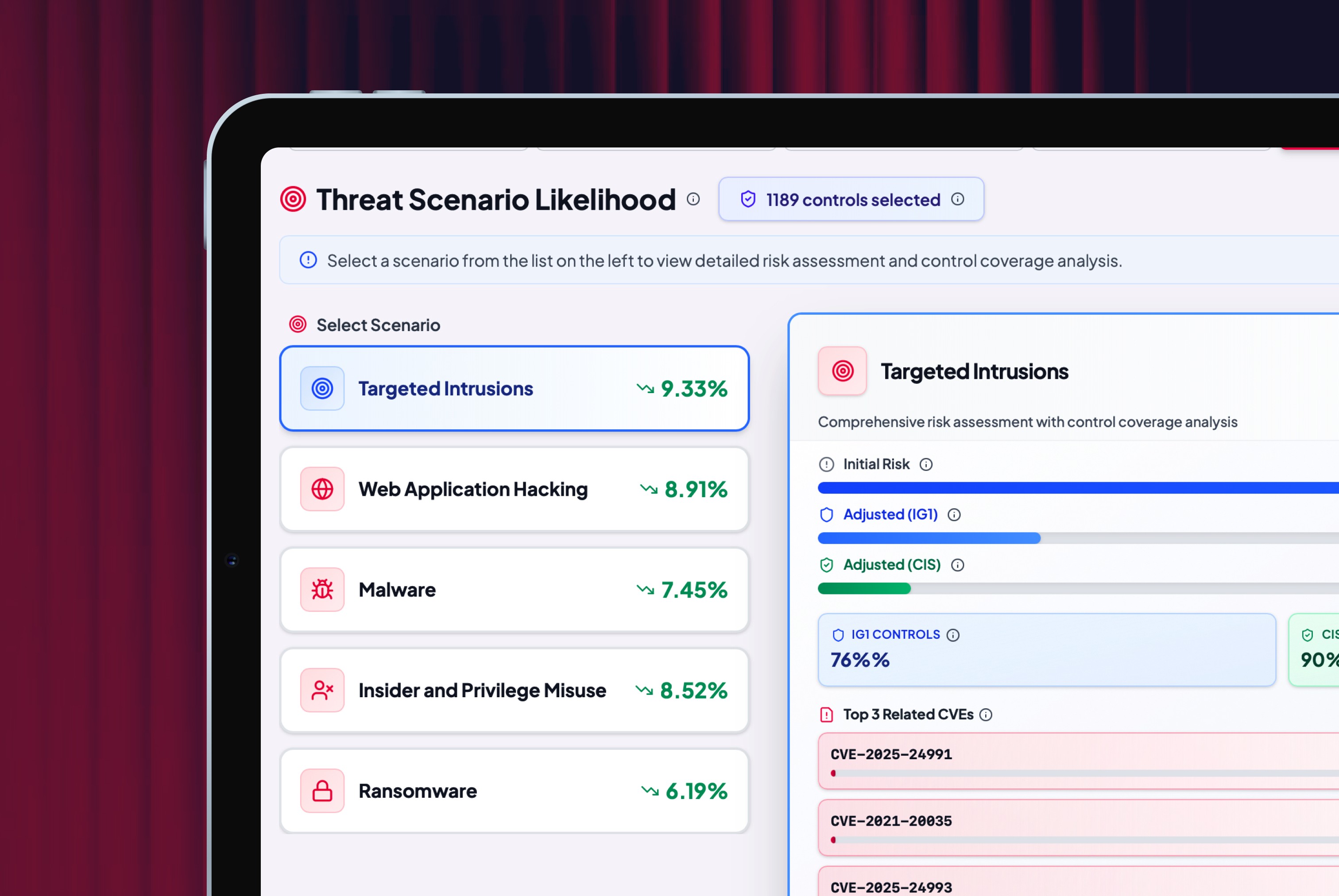
Scenario Engine
Scenario Engine
Model Attacks Before
They Happen
Model Attacks Before
They Happen
Run ransomware, BEC, cloud outage, supply chain, and zero-day scenarios against your actual infrastructure. Each scenario produces financial exposure estimates calibrated to your controls, asset values, and industry benchmarks.
Run ransomware, BEC, cloud outage, supply chain, and zero-day scenarios against your actual infrastructure. Each scenario produces financial exposure estimates calibrated to your controls, asset values, and industry benchmarks.
Run ransomware, BEC, cloud outage, supply chain, and zero-day scenarios against your actual infrastructure. Each scenario produces financial exposure estimates calibrated to your controls, asset values, and industry benchmarks.
ROADMAP
ROADMAP
Built for the next risk surface, not just the current one.
Built for the next risk surface, not just the current one.
The world is rightly spooked by agentic AI — Mythos, Claude, GPT-class agents — and the new categories of breach risk they introduce. Most security programmes haven't started measuring this exposure.
Most cyber tools weren't designed to. Astragar's quantification engine is being extended to bring agentic AI threats into the same financial-impact framework as everything else — so when your board asks the question, you already have the answer.
Bottomline: Claude Mythos, or any other Agentic AI system cannot exploit vulnerabilities that do not exist or were fixed. We help you plug the most impactful vulnerabilities first, regardless of their CVSS or EPSS score.
The world is rightly spooked by agentic AI — Mythos, Claude, GPT-class agents — and the new categories of breach risk they introduce. Most security programmes haven't started measuring this exposure.
Most cyber tools weren't designed to. Astragar's quantification engine is being extended to bring agentic AI threats into the same financial-impact framework as everything else — so when your board asks the question, you already have the answer.
Bottomline: Claude Mythos, or any other Agentic AI system cannot exploit vulnerabilities that do not exist or were fixed. We help you plug the most impactful vulnerabilities first, regardless of their CVSS or EPSS score.

FAQs
FAQs
Answers to your questions
What does Astragar do?

What does Astragar do?

What does Astragar offer?

What does Astragar offer?

Are vulnerability details shared with carriers or brokers?

Are vulnerability details shared with carriers or brokers?

Is Astragar a licensed insurance broker or agent?

Is Astragar a licensed insurance broker or agent?

Does Astragar replace vulnerability scanners?

Does Astragar replace vulnerability scanners?

How is Astragar different from point security or compliance tools?

How is Astragar different from point security or compliance tools?

Can Astragar support third-party and vendor risk visibility?

Can Astragar support third-party and vendor risk visibility?

Which compliance frameworks does Astragar support?

Which compliance frameworks does Astragar support?

How can I get started?

How can I get started?


Get Started Now
Get Started Now
Be ready for threats from misuse of Mythos or other AI Agentic solutions